Gain comprehensive visibility and control of your data with Logsign. Automate & orchestrate detection and response processes for faster response and improved workforce efficiency.
Logsign provides comprehensive visibility and control of your data lake by allowing security analysts to collect and store unlimited data, investigate and detect threats, and respond automatically.

Start data ingestion as soon as you deploy Logsign SIEM. Integrate all your security tools without vendor concern. Logsign classifies, normalizes, and enriches the data for effective use.
Investigate and hunt hidden threats, validate threat levels, and triage. Easy to search and filter your results with Lucene queries.
Detect attacks, lateral movements, and data leakage and loss. Triage them to reduce noise.
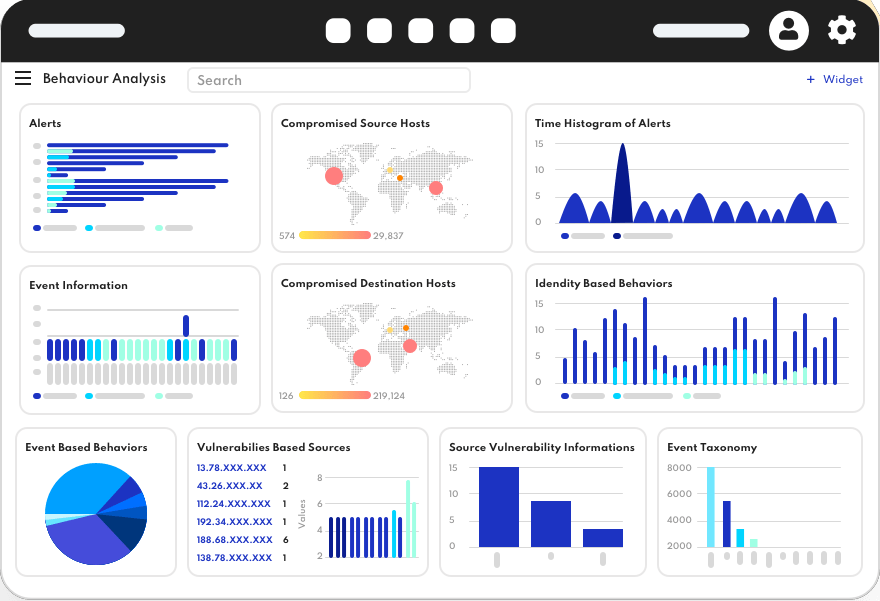
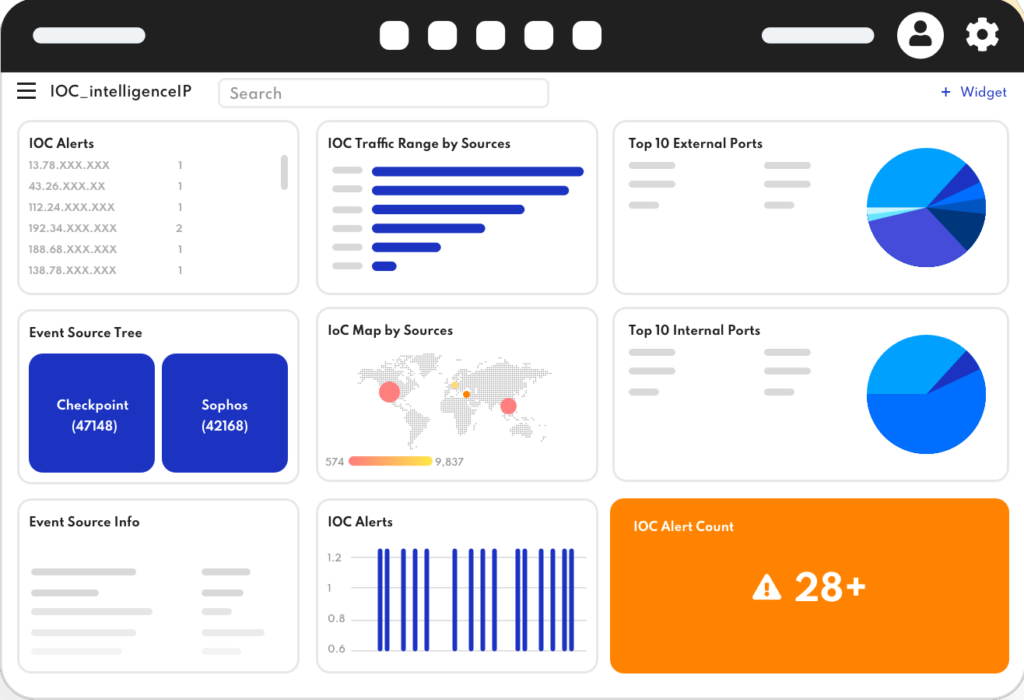
You can’t manage what you can’t see. Logsign empowers visualization with its security analytics-driven, built-in dashboards, and reports.
Mitigate and eradicate threats before they cause damage and disruption.
Logsign SOAR connects people, processes, and technology to effectively manage and streamline your security operations. Automate security devices and guide your team in the same direction to keep work flowing, investigate better, and respond faster.
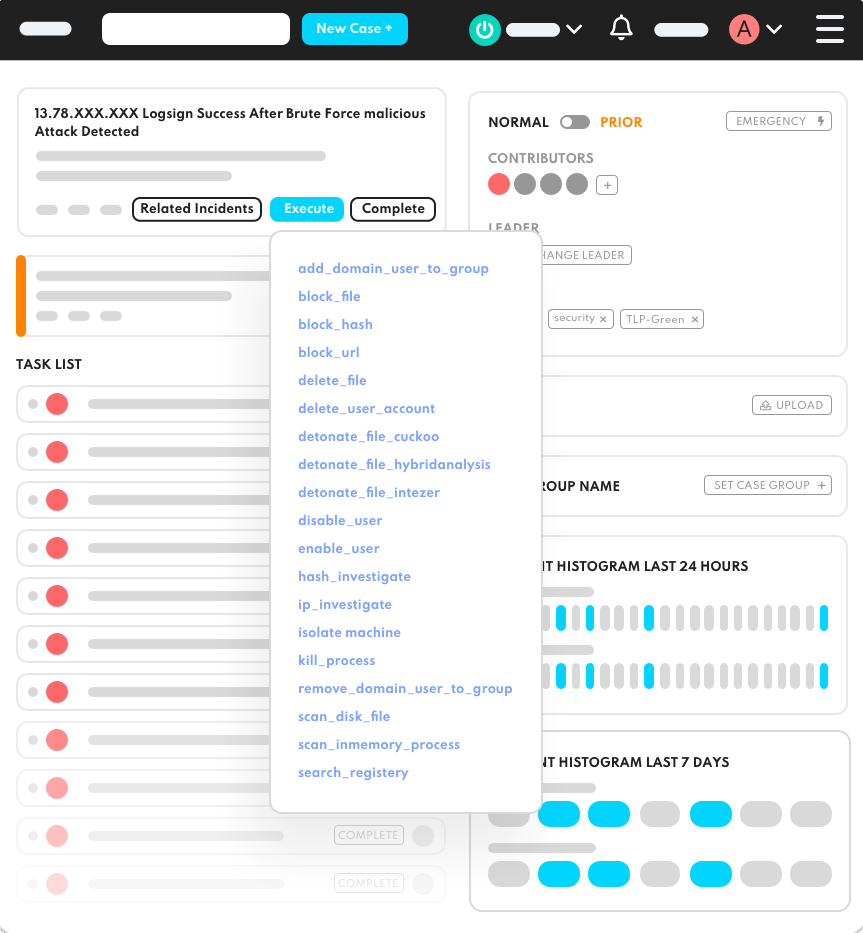
Automate time-consuming repetitive tasks and keep security analysts on the same page with interactive case management. Manage end-to-end incident life cycle in harmony.
Investigate alerts and validate threat levels. Triage them to reduce the false positives. Respond in seconds not hours.
Logsign SOAR is an independent platform, so there is no limit or barriers in integrating any security tools that you use in your SOC operations.
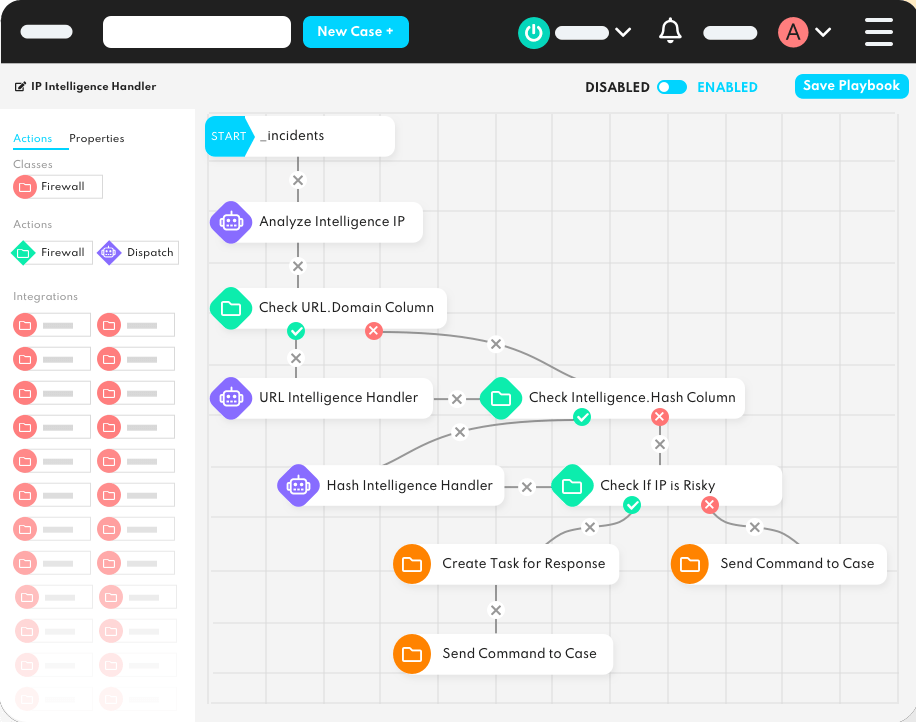
Logsign bots and playbooks are designed smartly to enhance your security analysts, not replace them. Save time for your overloaded analysts by using force multiplier bots and playbooks, and creating, automating, and orchestrating dynamic workflows.
Investigate, communicate and respond on a single screen to shorten your analysts’ learning curve and response time. Comprehensively manage incident life cycles from a single pane of glass.
Protect your business with our expert cybersecurity and cloud services. From penetration testing to compliance and SOC monitoring, we’ve got you covered.