ThreatCop is an AI/ML-based social engineering simulation and awareness tool that assesses the real-time threat posture of an organization from the people’s point of view. It is a SaaS/On-premise (in-house) security attack simulator. It can access the real-time threat posture of an organization from the people’s point of view and reduce the cyber risk up to 90% in 30 Days. It simulates the 6 biggest social engineering threats – Phishing, Ransomware, Cyber scams, USB, Vishing & Smishing.
ThreatCop follows a 4 step process. In the first step, these attack vectors are simulated in real-time to examine the employee vulnerability score. Based on the employee vulnerability score, the platforms help with imparting knowledge with security awareness training. The third step assesses the cybersecurity knowledge of each employee. It again simulates the attack vectors but in a totally different approach from the first simulation. This 4-step cycle goes on for each attack vector. ThreatCop presents an accurate real-time threat posture of the organization to the CXOs and helps reduce cyber risk.
Top 6 dummy cyber-attacks including phishing, smishing, vishing, cyber scam, risk of removable media, and ransomware.
Educate and train employees with awareness videos, gamified quizzes, posters, newsletters, and much more.
Analyze employees’ level of awareness post knowledge imparting with interactive assessment sessions.
With this social engineering simulation tool, you can assess an organization’s security posture, simulate the top 6 cyberattacks, train employees with 2,000+ cybersecurity awareness content libraries, assess employees’ vulnerability level with interactive assessment, and monitor and analyze results.
Knowledge imparting is a very essential aspect of the tool. Informative material including intuitive videos, Newsletters, Advisories, Case studies is provided to employees. These modules are customized according to the simulated attack in a campaign.
Employees are not only provided with informative content but also, their acquired knowledge is tested with regular assessments. This includes assessment modules for each employee with a different version of a questionnaire related to the deployed simulated attack during the campaign. Periodic reminders are sent to those employees who do not complete these assessments. Employees who are unsuccessful in performing well during the assessment must go through the retest. A certificate is provided to those employees who pass the assessment.
It is deployed as per the convenience of the client. It can be provided as Software as a Service solution, as an in-house solution, or as managed service. It allows the data to remain within the organization.
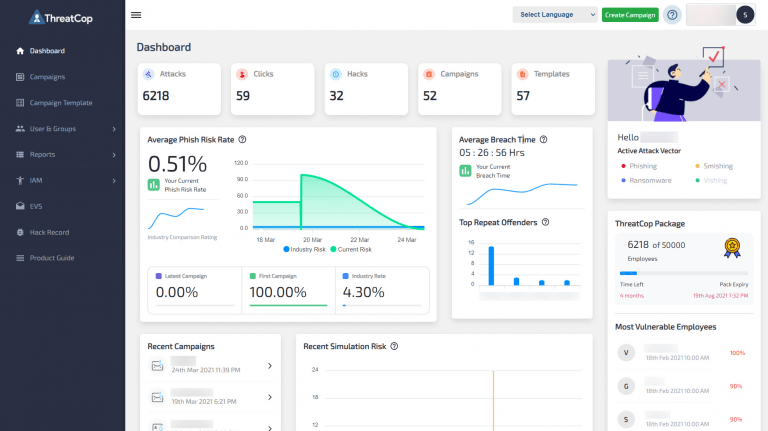
It has a real-time dashboard that provides detailed analytics on the progress of employees. Administrators can keep a track of employees’ vulnerability measures. This will allow administrators to employ measures that can help in improving employees’ responses to cyber-attacks.
The continuous process of cyber-attack simulation and creating awareness with knowledge imparting on a regular basis enables employees in identifying different tactics that are used by cyber-criminals.
This is extremely crucial since 90% of all cyber-attacks occur due to the negligence of employees. With its four-step cycle, the product ensures that the weakest link of the information security becomes a shield against cyber-attacks in an organization.